Security Where Needed
with Cloud-Managed SASE
For instance, traffic bound to the Internet will need secure web gateway capabilities such as URL filtering, malware scanning, and data exfiltration detection. For user traffic going to the public cloud, one may want to scan assets for sensitive data for compliance and will need features like CASB for SaaS applications. It is critical to apply security controls based on the context while ensuring a good user experience. While inline technologies work best for access control, low and slow advanced threats can only be detected with more sophisticated analysis of data patterns over prolonged periods of time. Observability to the traffic pattern variations can ensure detection of anomalous behavior.
This distributed data plane architecture is based on a combination of intelligent ‘services PoPs’ as well as cloud-managed edge devices, with both hosting security functions. A service PoP goes beyond conventional connectivity services in supporting scale-out compute and storage required for SASE functions. Paired with the distributed data plane is effective control.
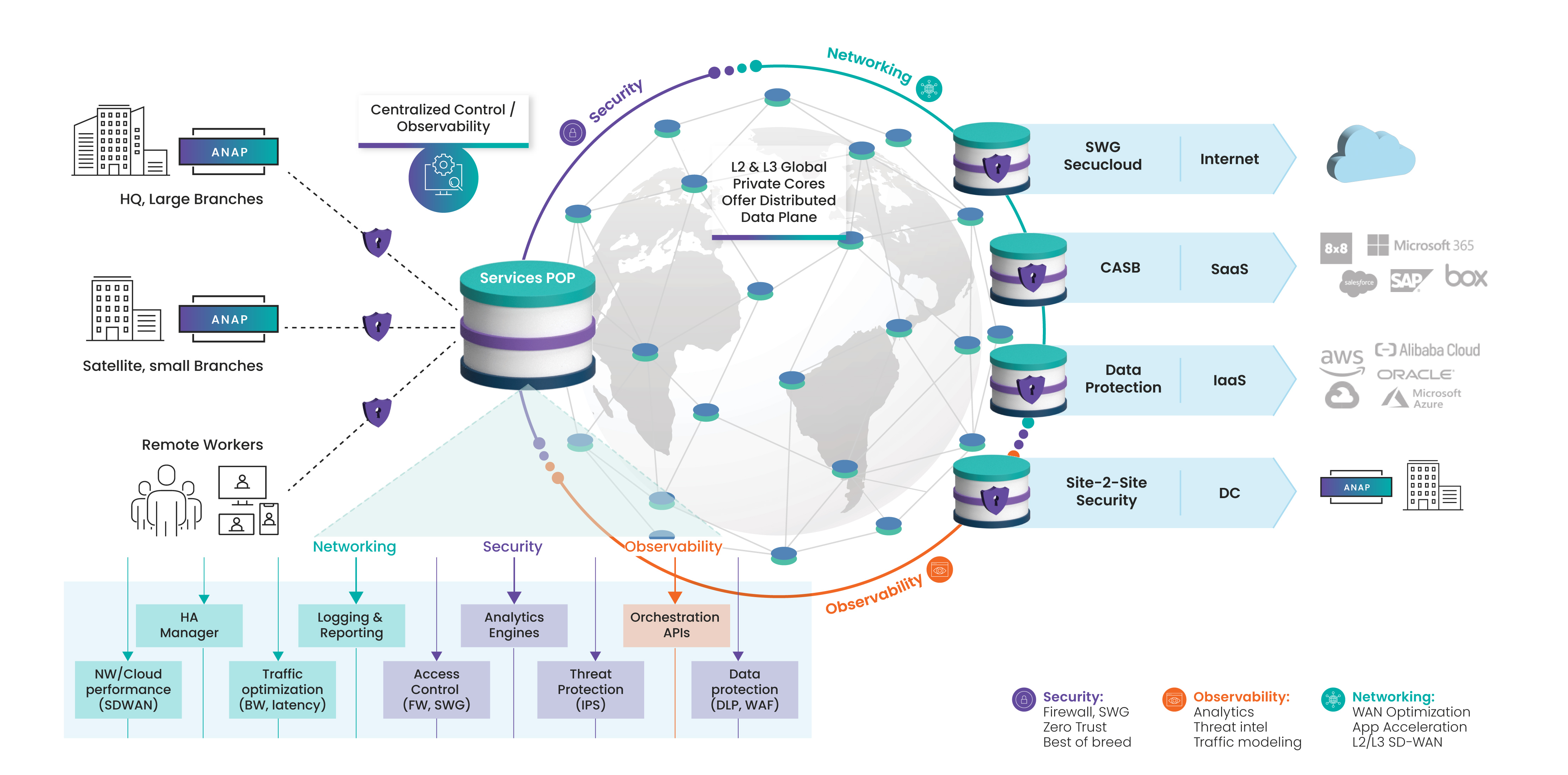
Figure 2: Going beyond conventional connectivity
click to enlarge
Unified control plane
SASE must be centrally orchestrated, a unified control plane that ties these capabilities together in a coherent way to apply policies consistently across hundreds of locations and ensure they get applied properly. As is common knowledge, the main reason for security breaches is misconfiguration due to complexity, lack of knowledge, and lack of oversight. Without a unified control plane, it is hard or even impossible to apply security ubiquitously and consistently. Given the as-a-service aspect of SASE, a managed services provider may effectively offer this control, removing the burden and chance of misconfiguration from the IT department.
‘Single pane’ management
The third technology underpinning is single pane management and observability in support of both network and security services. This is the ability to provide visibility into performance characteristics and security aspects of the traffic, and there are multiple locations across the network where this capability resides. As part of the managed services, the NOC/SOC will have visibility across the deployment, with the ability to leverage AI/ML and data analytics for proactive issue identification and resolution. The enterprise also requires a role-based portal into its slice of the network, and any management tools must interface with one or more logging applications.
Operational aspects
Organization structure
One of the main challenges cited as a cause that gets in the way of the SASE dream is the current structure of the organization. Typically, network decisions are made by network teams, and security decisions are made by security teams. But this



















